What You Should Know About the Thunderstrike Mac Bootkit
A researcher has developed a nasty bootkit capable of taking complete control of OS X devices. Here is what you need to know.
138 articles
A researcher has developed a nasty bootkit capable of taking complete control of OS X devices. Here is what you need to know.
Children are crazy about tablets but it is important to set limitations in order to prevent it from becoming a real obsession. Here are a couple of tips to help you tame your child’s iPad.

In this episode of the Talk Security podcast, Threatpost’s Chris Brook and Brian Donohue discuss the Dark Hotel cyberespionage campaign and the WireLurker Apple malware.

Yesterday, researchers disclosed a powerful iOS vulnerability that is responsible for the WireLurker Apple malware.

Let’s take a look at the security features in the new version of Mac OS X – Yosemite. Apple certainly makes a decent effort.

Apple malware targets iOS by infecting OS X machines and then swapping legitimate apps for malicious ones as soon as an iOS device connects via USB.

Google’s mobile operating system joins Apple’s iOS in offering full disk encryption by default to all users in its newest version — Android 5.0 aka Lollipop.

Even when your iPhone is in your hands or on the table, it can reveal some of your secrets to strangers. Here are 10 tips to prevent this from happening.

Virus Bulletin is a traditionally enterprise-focused event, but each year topics of consumer interest, like Apple malware, hackable devices and Bitcoin are presented.

iOS-based devices have a large share in the enterprise, which assures a strong demand for BYOD-oriented security features. A number of them arrive in iOS 8.

With the release of iOS 8, Apple claims it can’t access the personal data on your iPhones and iPads and it can’t give it to authorities. But it seems there’s a catch.
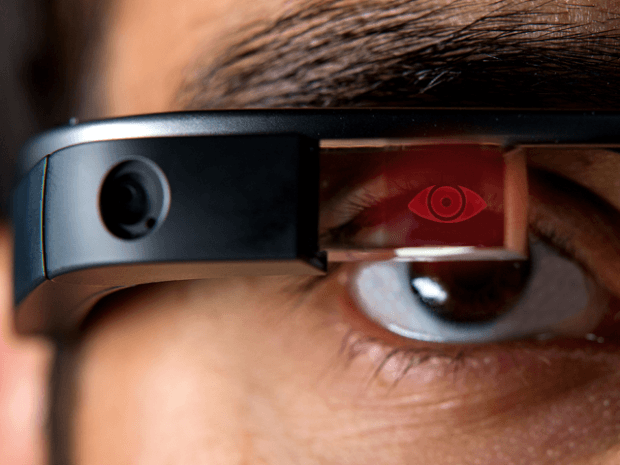
New mobile and wearable devices offer users a robust set of innovative features and utilities but they often face the same traditional threats as old fashioned computers.

The biggest concern about Apple Pay is that one’s iCloud account now controls not only private photos, app data, and messages, but also money. You lose your password – you lose everything and as the celebrity hack showed us, there is no need to hack Apple’s servers. Social engineering, phishing, trojans – all cybercriminal tools will now be targeted at people’s electronic wallets.

The Apple iCloud nude celebrity photo fiasco underscores the uncomfortable reality that even the savvy among us aren’t totally sure about what goes on and into “the Cloud.”
Don’t want your private photos or credit card posted somewhere on the web? You should rethink your approach to cloud services then.

How iOS 8 and Tizen releases affect smartphone market and security landscape.

Adults can choose to face the financial consequences of their own actions, but they may want to know how to prevent their kids from running up exorbitant credit card bills tied to the parents’ iTunes or Google Play accounts.

App stores offer all the promise of a virtually unlimited range of games and tools, but are rife with pitfalls too. These include bad apps, ballooning costs, and malicious apps, particularly on Android devices.

Apple has announced new versions of its operating system. OS X and iOS become closer, gradually merging into a single environment. How well is it protected?

A new piece of ransomware targeting Apple users emerges along with a hybrid malware combining Zeus and Carberp. There’s also an issue with the Spotify Android app.
New ransomware targets Apple users running iOS mobile and O SX Mac devices with a piece of malware that blocks use and demands payments.