
What is a hoax, where do hoaxes come from, and why are they dangerous?
What the Hoax verdict means, and why such software is becoming more of a problem.
3758 articles

What the Hoax verdict means, and why such software is becoming more of a problem.

A new spam mailing threatens the reputations of small businesses websites.

Digital signatures cannot solve the requirement of checking the authenticity of documents required by KYC procedures. That is where smart contracts may come in handy.

The updated version of Kaspersky Safe Kids addresses three typical parental control issues.

Eugene Kaspersky’s thoughts on the latest updates to our Earth 2050 futurological project.

A guide on how to protect your account against spammers, hackers, and other gate-crashers.
Scammers are using Google Calendar, Photos, Drive, and other services to distribute spam. Here’s how it works.

Scammers posing as CIA agents demand ransom for alleged possession of child porn, threatening arrest.

Eugene Kaspersky on why Kaspersky Lab became simply Kaspersky — and the plans behind that change.

A guide on how to disappear from Snapchat but keep the mementos you want.

We explain what file types cybercriminals most often use to hide malware, and how to avoid getting infected.

For three weeks, Baltimore’s administration has been struggling with the aftermath of a ransomware attack.
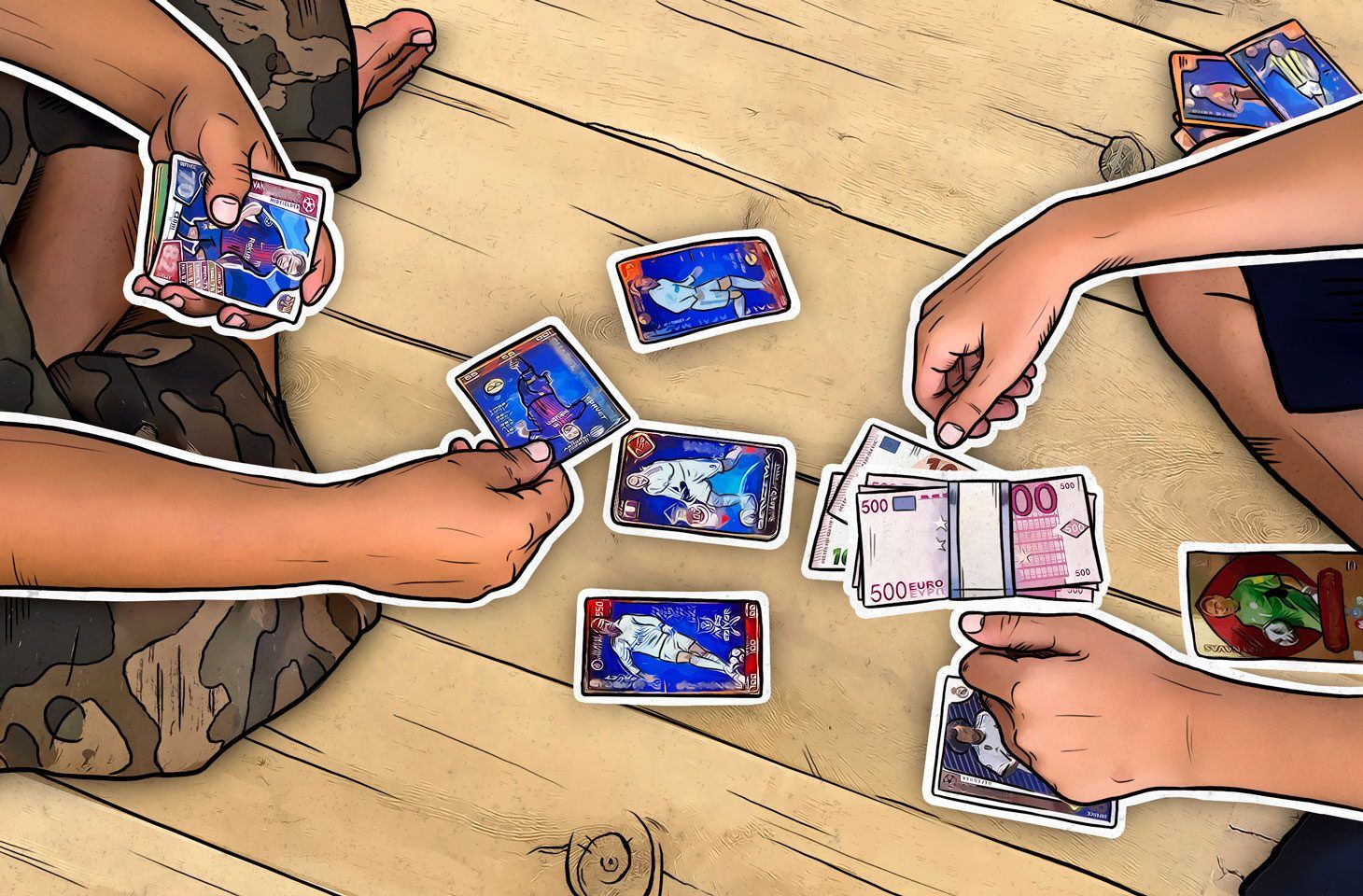
How to steal a million (OK, half a million), or what happened to the Boca Juniors
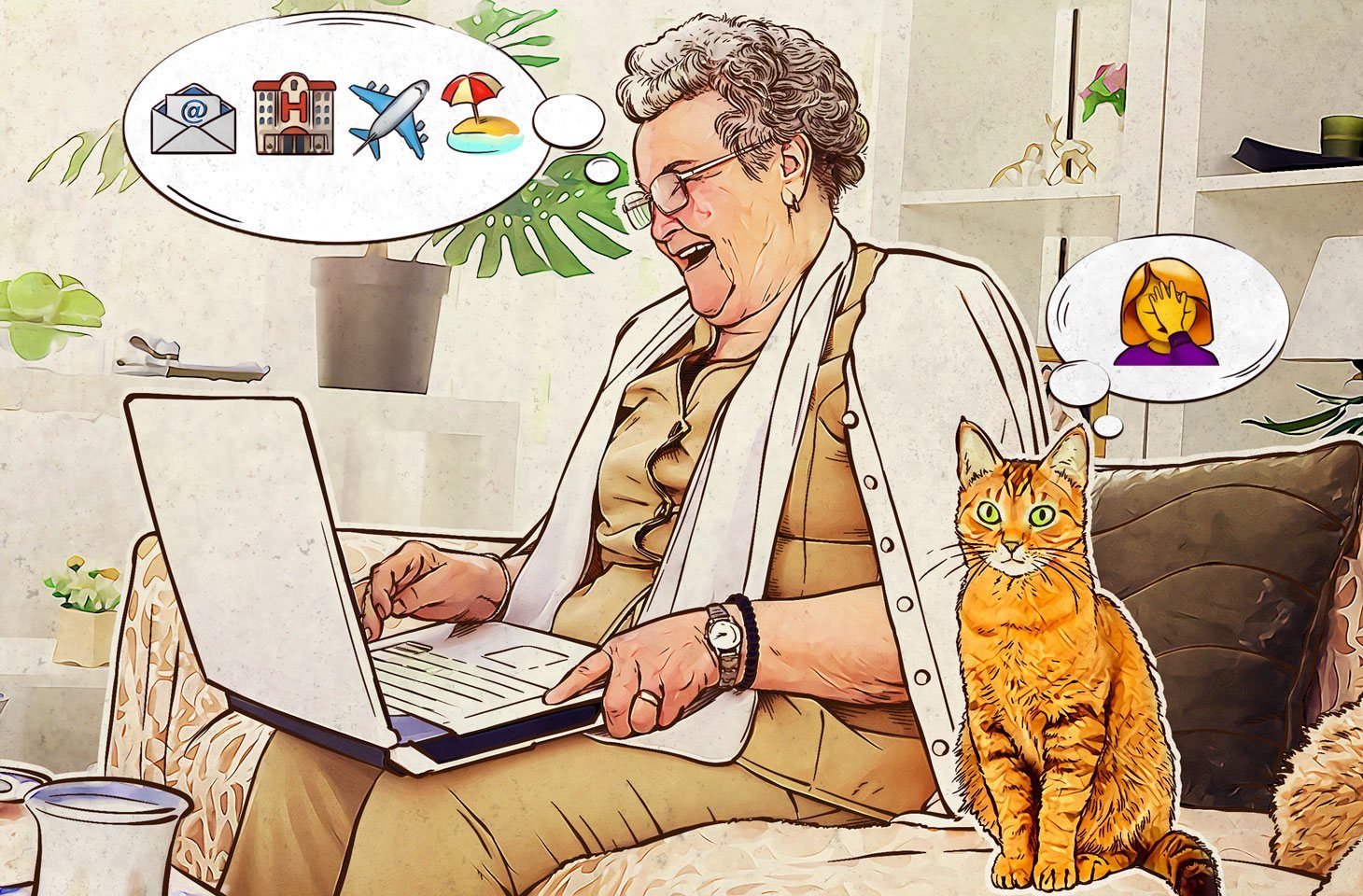
No matter how good malefactors are at pretending to be the real deal, you can still spot travel phishing if you know these three simple rules.

Emulator in Kaspersky Lab products: what is it and why it’s so important for antivirus to have one.

5 quick tips for (moderately) paranoid people on how to ensure security and privacy while traveling.

Tempted to stream Game of Thrones free? Be very cautious: You might pay for it with your passwords and credit card details.


To protect themselves, businesses need to take a proactive approach, constantly adapting their security controls to the ever-changing threat environment.

How to expose fake news bots based on their behavior and what insights one can get while doing this.