The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.co.za/blog/tag/securityIS
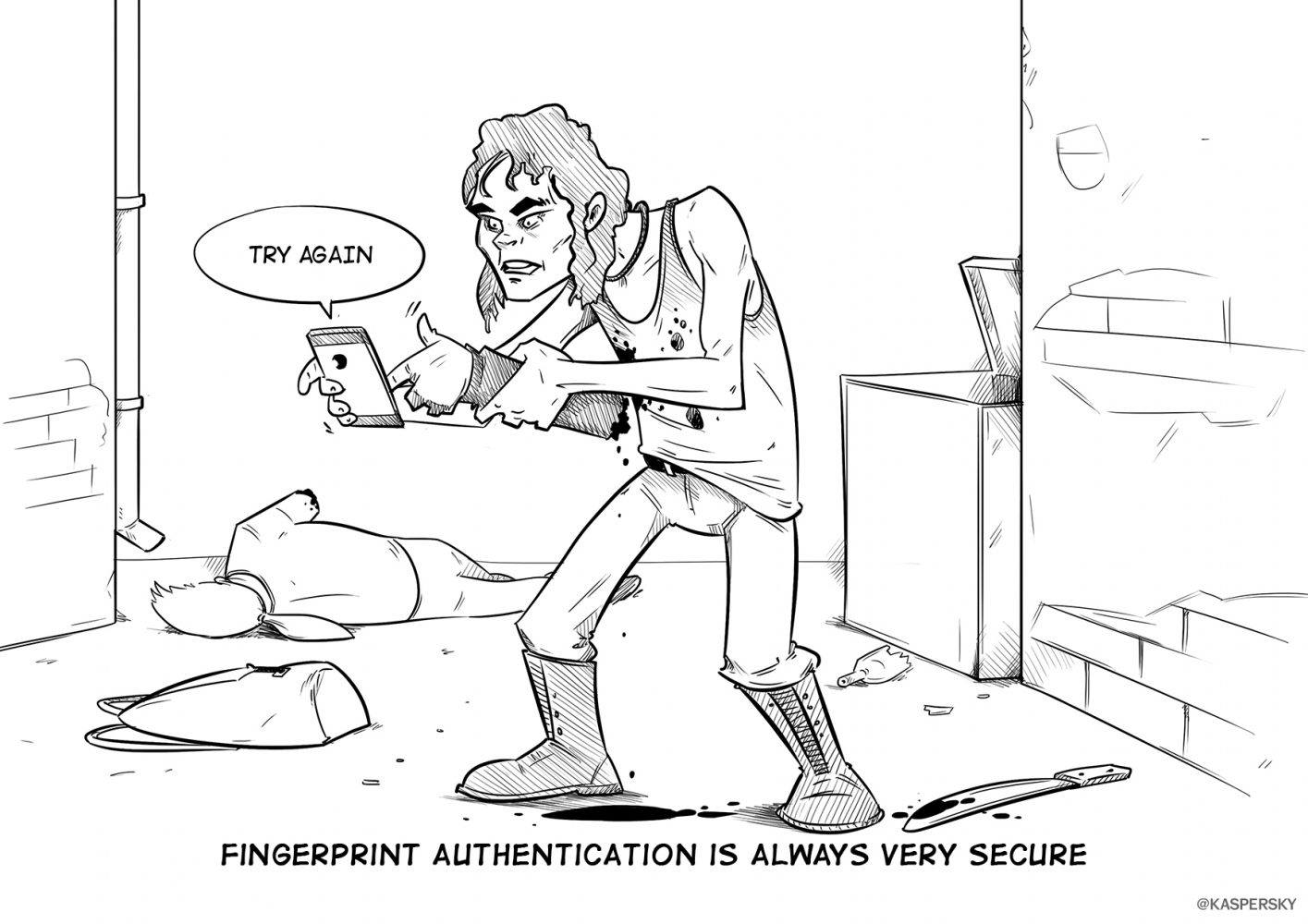
He didn’t know he could just enter a PIN code with his own hand.
The next page of The Сyberworld Survival Guide. The entire guide can be found here: http://www.kaspersky.co.za/blog/tag/securityIS
The next page of The Сyberworld Survival Guide. The entire guide can be found here: https://www.kaspersky.co.za/blog/tag/securityIS
He didn’t know he could just enter a PIN code with his own hand.

Microsoft’s announcement that it is going to consolidate all of its major platforms into one is quite a logical move. But what are the possible consequences regarding businesses and cybersecurity?

We break down the BeatBanker trojan attack, which combines espionage, crypto theft, and mining with inventive ways to dig its heels into a smartphone.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.
Learn how to spot deepfakes in photos, videos, voice messages, and video calls in real time.
Our Android apps are no longer available on Google Play. We explain how to download, install, and update them by alternative means.