
Apparent reasons: a few examples of why IT security breaches happen
Over the last few years we have witnessed a number of high-profile, large scale security breaches with quite dramatic consequences, such as massive leaks of personally identifiable data.
 security breaches
security breaches
 figures
figures spam
spam





 cryptolocker
cryptolocker

 enterprise security
enterprise security


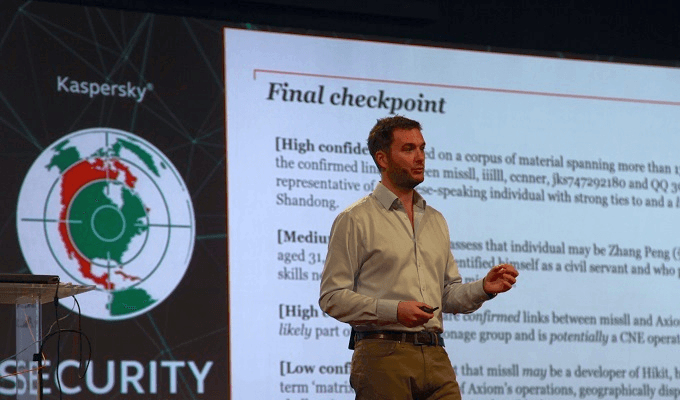
 FalconsAPT
FalconsAPT


