
News
1073 articles

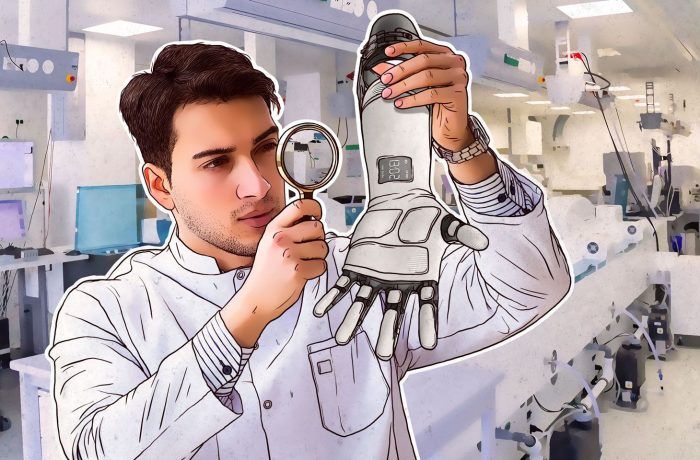
A helping hand for a smart hand: How we hacked it so others wouldn’t
At Mobile World Congress 2019, our experts presented a study on the security of Motorica smart artificial limbs.

Cybercriminals intercept codes used for banking to empty your accounts
Crooks hacked telecom protocol SS7 to steal banking two-factor authentication codes.

Crazy Razy, bitcoin thief
The Razy Trojan secretly installs malicious extensions for Chrome and Firefox to serve phishing links and steal cryptocurrency.

My data was leaked in Collection #1. What should I do?
A huge database of leaked e-mails and passwords surfaced in the Internet. Here’s what you should do about it.

Printers gone mad
50,000 printers worldwide suddenly printed a leaflet in support of youtuber PewDiePie. How can you protect your printer from hackers?

Holiday shopping and holiday phishing
The winter sales season is the hottest time of the year for shoppers and financial phishers. Be careful!

Twitter cryptocurrency scams: A hundred Elon Musks — and now Target
Twitter cryptocurrency scams are becoming more and more advanced and convincing, with scammers using new techniques and some heavy artillery.

Killer messages on Sony PlayStation 4 and how to deal with them
One short message is enough to send a Sony PS4 into an infinite restart loop. Here’s how to deal with it.

No, your account on Facebook was not hacked
The “another friend request from you” hoax on Facebook is gaining traction. Don’t fall for it.

What do you need to do about the recent Facebook security breach?
Facebook has been breached, and malefactors gained access to some 50 million accounts. We offer some quick tips for your safety.

8 fun facts about fax. Yes, fax!
Which is older, the phone or the fax? Is it true that no one faxes anymore? And can a fax machine be hacked? (Spoiler: yes)

5 Fortnite security tips
Fortnite for Android is not available on Google Play. We explain how to download and install it properly, and what else to do to stay safe.

Avoid pitfalls when backing up your WhatsApp chats
WhatsApp for Android can back up your chats to Google Drive. It’s free, but it may hurt older backups. Here’s how to get it right.

Man-in-the-Disk: A new and dangerous way to hack Android
How a seemingly harmless Android application can infect your smartphone using shared external storage.

IoT security leads to legal headaches
Are the IoT’s security issues placing the industry on the road to a litigation nightmare?

How risky is the Internet? Researchers say 42%
Almost half of the most-visited websites open visitors to potential dangers. What can you do?

Hijacking online accounts through voicemail
When it comes to online accounts, voicemail is a major security hole. Here’s why.

KeyPass: Ravenous ransomware
KeyPass ransomware is infecting computers worldwide, encrypting almost everything in its path. And it all starts with downloading a seemingly innocuous installer.

On the hunt for Twitter bots
How security researchers were able to track down cryptocurrency bots on Twitter.
 Android
Android 2FA
2FA extensions
extensions scam
scam
 gamers
gamers Facebook
Facebook