
Hidden miners on Google Play
Hidden miners detected in soccer and VPN apps on Google Play — steer clear!
137 articles

Hidden miners detected in soccer and VPN apps on Google Play — steer clear!

Most computer infections come from visiting porn sites, or so some people say. Are they right?

Sex sells, as they say in advertising. In cyberspace porn serves as one of the most popular tools for malicious activity.

Our infographics will help you find the security solution that suits you best.

Do border agents have the right to search your devices? How can you protect your data from searches at the border? We have 11 tips covering this topic.

Kaspersky Free Antivirus provides reliable and, yes, free protection for Windows machines
What miners and Web miners are, why you need to protect yourself, and how Kaspersky Lab products can assist


The CryptoShuffler Trojan does its utmost to go unnoticed, stealing Bitcoins on the sly.

Our research shows most users of online dating sites fudge information about themselves. Why they do it and what you can do about it.

The Internet of Things is vulnerable like nothing else. What should you do to secure your smart home and other devices on the home network?

The global launch of our free antivirus utility has prompted a bunch of questions and resurrected a couple of ancient myths.

Living online is more comfortable than ever — do you really still need a helmet?


By now, everyone has heard about the WannaCry ransomware attack. So far we have two posts about it: one with a general overview of what happened, and another with advice

Kaspersky Safe Browser for iOS lets you filter unwanted content — violence, adult materials, drugs, and more.

Thanks to Tinfoil Hat Day, people all over the world have learned how to shield their brains from invisible foes.
Many people now do their taxes online, and cybercriminals see that as a huge opportunity to make money with phishing schemes.
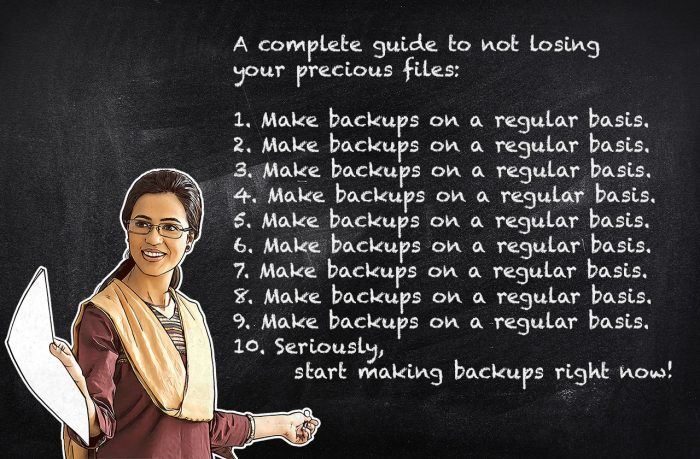
The 10 essential steps that can reliably protect important files.

Kaspersky Safe Browser for iOS protects you from phishing, malicious sites, and spammy links.

The My Kaspersky website gives you remote control over the security solutions on all of your devices.