
Geolocation data brokers: What they do and what happens when they leak
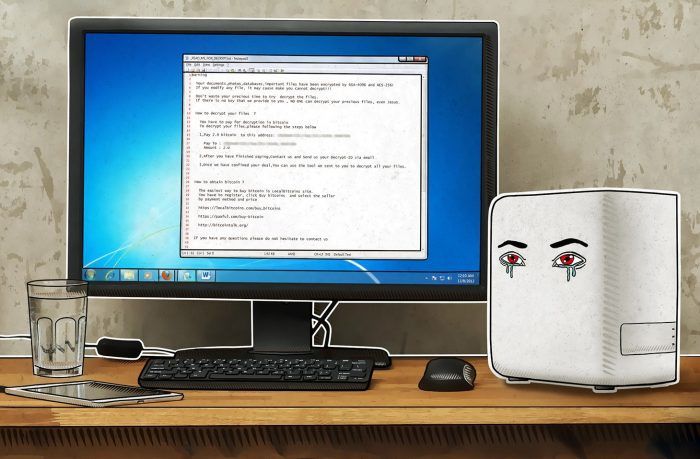
The recent leak at major location-data broker, Gravy Analytics, shines a light on the implications of mass location-data collection.
62 articles

The recent leak at major location-data broker, Gravy Analytics, shines a light on the implications of mass location-data collection.

A detailed guide to configuring privacy settings in the ASICS Runkeeper running app.

A detailed guide on setting up privacy in the adidas Running app.

A detailed guide to configuring privacy settings in the MapMyRun fitness tracker.

This guide will walk you through the essential privacy settings in the Nike Run Club training app.

Want to keep your runs, rides, and hikes private on Strava? This guide will walk you through the essential privacy settings in this popular fitness app.
Running apps know a lot about their users, so it’s worth setting them up to ensure your data doesn’t fall into the wrong hands. Here’s how.

What security aspects should be top-of-mind when implementing important changes in corporate IT infrastructure?

Low-code apps lower IT costs, but boost information security risks. How to mitigate them?

Researchers have come up with a way to exfiltrate confidential data by observing LED activity.

A method of stealing data from an air-gapped system through a speaker you may not even know is there.

A recent study shows that even “clean” Android smartphones collect a lot of information about their owners.

Computers don’t necessarily need a Wi-Fi module to transmit information over Wi-Fi, Israeli researchers have found.

Our experts uncovered a scheme to extract cardholder data using Google tools.

If you don’t want to pay for extra gigabytes in iCloud, try these other ways to backup your photos and other iPhone files.

Employees going away for the winter break? We explain what to do to keep trips from turning into corporate data leaks.

We created a new service that can provide a detailed dossier on any file Kaspersky Lab’s systems have encountered.
How to safeguard your solution and clients with time-tested technologies.


Do border agents have the right to search your devices? How can you protect your data from searches at the border? We have 11 tips covering this topic.
Do you use NAS for backup? We’ll tell you how to protect it from new threats