
Breathing new life into old gadgets for a better home office
Create a digital comfort zone using any old tablets, laptops, and modems you have on hand to work from home safely.
3758 articles

Create a digital comfort zone using any old tablets, laptops, and modems you have on hand to work from home safely.

Our technologies prevented an attack. Expert analysis revealed the exploitation of two previously unknown vulnerabilities. What you need to know.

Your online finances need proper protection. Learn how to secure your PayPal account.

A detailed look at a phishing site masquerading as an e-mail scanner and its attempts to snag victims.

Life has made a dramatic shift online in 2020. Our solutions will help you avoid unnecessary stress in the new reality.

You can refuse some permissions to greedy games, and they most definitely do not need these five.

Many services allow you to share your subscription with family. Here’s how popular sites handle sharing.

Our experts’ detailed analysis of the prime suspect in the ransomware attack on Garmin.

What is Zero Trust, and why is it attractive for modern business?

It’s a new speedrunning world record — made with Kaspersky Internet Security working in the background.

The Lazarus cybercrime group uses traditional APT techniques to spread VHD ransomware.

A preview of Black Hat 2020 with Eugene Kaspersky, Kurt Baumgartner, and Costin Raiu.

You can design a digital comfort zone you won’t want to leave.

Our experts detected a malware framework that cybercriminals use to attack various operating systems.

What you need to check regularly to keep your Android smartphone and your data safe and sound.

Our new VPN has a failsafe — if it can’t protect, you can’t connect.

We examined the contents of Kaspersky’s CEO’s spam folder to find out what spammers and phishers think might entice him.
Microsoft has released a patch for a critical RCE vulnerability in Windows Server systems.

The Safe Search in YouTube feature prevents children from stumbling across violent, sexual, and other unwelcome content.
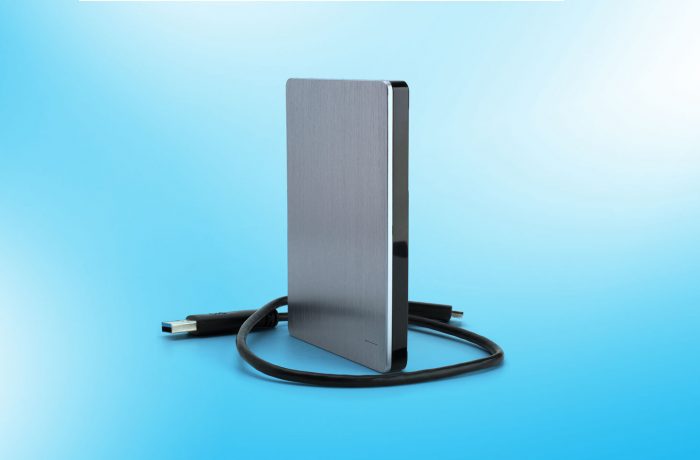
We explain why you need to back up critical data, even if you trust your equipment 100%.