VIRUS DEFINITION
Virus Type: Virus / Malware
Also called: Backdoor.MSIL.Tyupkin
What is Tyupkin ?
Tyupkin is a piece of malware that allows cyber criminals to empty cash machines via direct manipulation. This malware, detected by Kaspersky Lab as Backdoor.MSIL.Tyupkin, affects ATMs from a major ATM manufacturer running Microsoft Windows 32-bit.
Virus Threat Details
The cyber criminals work in two stages:
Stage 1 –Access and Infection
First, they gain physical access to an ATM and insert a bootable CD to install the malware – code named Tyupkin (Backdoor.MSIL.Tyupkin). Once the ATM system has been rebooted, the infected ATM is under their control.
Stage 2 – Control and Theft
The infected ATM then runs in an infinite loop waiting for a command. In order to make the scam harder to identify, Tyupkin malware only accepts commands at specific times on Sunday and Monday nights. It is during those times that the cyber criminals are able to steal money from the infected machine.
Methodology
Video Footage obtained from security cameras at the infected ATMs showed the methodology used to access cash from the machines. A unique digit combination key based on random numbers is freshly generated for every session. This ensures that no person outside the gang could accidentally profit from the fraud. Then the malicious operator receives instructions by phone from another member of the cyber-criminal gang who knows the algorithm and is able to generate a session key based on the number shown. This ensures that the mules collecting the cash do not try to go it alone.
When the key is entered correctly, the ATM displays details of how much money is available in each cash cassette, inviting the operator to choose which cassette to rob. After this the ATM dispenses 40 banknotes at a time from the chosen cassette.
Where is the Tyupkin virus infecting ATM machines?
Based on statistics culled from VirusTotal, malware submissions have been seen from the following countries:
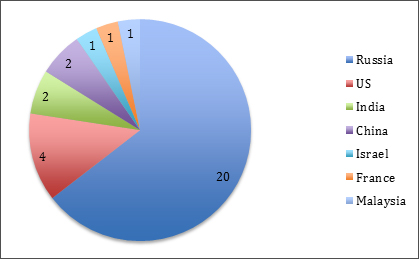
Countries where the Tyupkin malware is live
ATM Security Tips for Operators/Banks
- Review the physical security of their ATMs and consider investing in quality security solutions.
- Replace all locks and master keys on the upper hood of the ATM machines and do not consider using the defaults provided by the manufacturer.
- Install an alarm and ensure it is in good working order. The cyber-criminals behind Tyupkin only infected ATMs without security alarm systems installed.
- Change the default BIOS password.
- Ensure the machines have up-to-date antivirus protection
- Be on the lookout for social engineering attacks by criminals who may be masquerading as inspectors or security alarms, security cameras or other devices on premises.
- Treat intruder alarms seriously and act accordingly by notifying law enforcement authorities of any potential breach.
- For advice on how to verify that your ATMs are not currently infected, please contact Kaspersky at intelreports@kaspersky.com. To make a full scan of the ATM’s system and delete the backdoor, please use the free Kaspersky Virus Removal Tool (available to download here).
Video: Tyupkin ATM Security Breach
View the Tyupkin ATM Security breach video