
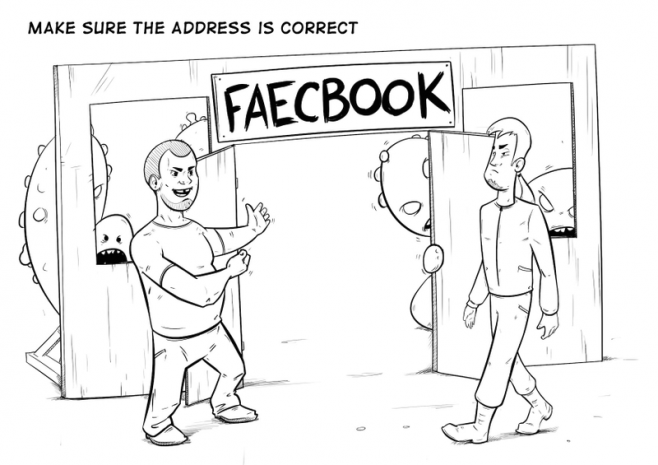
Avoid news-related phishing
Internet scammers are quite smart and greedy, and know how to disguise their traps, but there are always some ways to find out where these traps are.
921 articles

Internet scammers are quite smart and greedy, and know how to disguise their traps, but there are always some ways to find out where these traps are.

According to research by Kaspersky Lab, 22 percent of phishing scams on the web target Facebook.
The next page of The Сyberworld Survival Guide. The entire guide can be found here: http://www.kaspersky.co.za/blog/tag/securityIS

Last week was something of a slow week for those of us that spend our days writing about computer security news. However, while there may not have been an abundance
A few weeks ago Kaspersky Lab experts published a new study on the evolution of phishing over the past two years. Here is a summation of what the study found:

Phishing is a dangerous type of Internet fraud that uses fake websites to swipe user logins and passwords to hijack their online accounts to steal money or spread spam and

If you’ve used the Internet for more than seven minutes, you’ve probably been targeted by several hundred phishing attacks. Phishing, when attackers try to pry bank account numbers, codes and

Why do we have a love-hate relationship with dating apps, and what are they doing to our brains? Can an emoji start a war? Is marrying an AI actually a thing? We’re exploring how modern tech is redefining love and our very ideas of it.

We’re breaking down how to protect yourself from fake streams, counterfeit tickets, and non-existent merch — and how to keep your personal and financial data from being snatched during the 2026 Winter Olympic Games.
Breaking down core cybersecurity terms that colleagues often interpret differently or incorrectly.

Learn how to spot deepfakes in photos, videos, voice messages, and video calls in real time.

Detecting attacks related to compromised accounts with AI and other updates in Kaspersky SIEM.

NFC relay attacks, pre-installed Trojans, and other nasties ruining the Android experience in 2026.

Crooks are impersonating your brand to attack customers, partners, and employees. How do you spot — and stop — an attack of the clones?

How criminals exploit the familiar “tap your phone to pay” feature to steal your money.

Eight digital New Year’s resolutions you absolutely need to keep.

A new wave of ClickFix attacks spreading a macOS infostealer are posting malicious user guides on the official ChatGPT website by piggybacking the chatbot’s chat-sharing feature.

Here’s how to mitigate the risks of targeted attacks on your organization’s mail servers.
We’re going bargain hunting in a new way: armed with AI. In this post: examples of effective prompts.

Systematic measures and tools that organizations can use to defend against malicious browser extensions.