
How pirates hook gamers
The story of a guy who just wanted to download a pirated copy of a game but got malware instead. It’s happening more and more often, and we explain why.
3758 articles

The story of a guy who just wanted to download a pirated copy of a game but got malware instead. It’s happening more and more often, and we explain why.
Artificial intelligence assists judges, police officers, and doctors. But what guides the decision-making process?

Scammers are sending tons of YouTube direct messages pretending to be from top YouTubers. They’re phishing. Here’s how the scheme works.

Using only publicly available sources, how much can you find out about someone?

Things you should know about your home Internet connection: How to be sure it is safe and waste no time calling tech support.

We explain how ultrasound and audio recordings hidden in background noise can be used to control voice assistants.

When you’re ready to leave the privacy fever dream that is Facebook, make sure you have everything before you lock the door on your way out.

Crooks hacked telecom protocol SS7 to steal banking two-factor authentication codes.

Changing passwords regularly is outdated. Use strong and unique passwords that are easy to remember instead. Here’s how to make them.
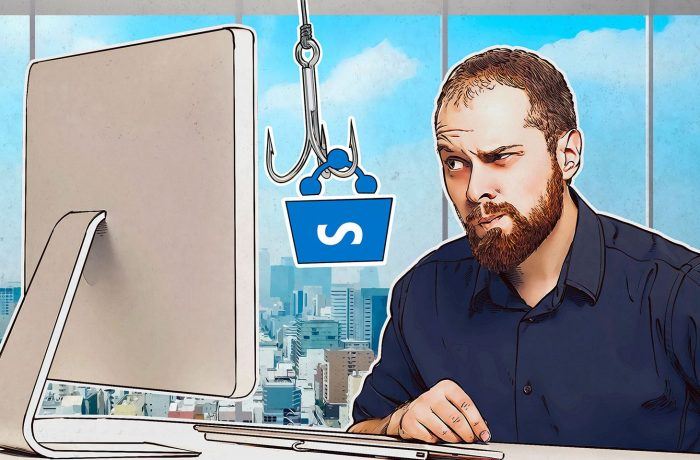
Cybercriminals are bypassing mail spam filters by hiding documents with a malicious link in SharePoint Online.

Analysis of a German sex toy reveals all sorts of vulnerabilities.

Our new partner program: What customers should know about Kaspersky United.

How do you explain the basic concepts of staying safe on the Internet to your kids? With a good book, of course!

Burnout caused by routine is a problem not only for employees, but for the entire company.

The Razy Trojan secretly installs malicious extensions for Chrome and Firefox to serve phishing links and steal cryptocurrency.


New iPhones support eSIM technology. We explain what it is and who will soon be using it.

WhatsApp and Facebook are swimming in links to ticket giveaways for fairs and airlines. Don’t get excited, though; the tickets are fake.

Ex-employees can go to extremes for the sake of revenge. How to terminate a work relationship safely and securely.

A huge database of leaked e-mails and passwords surfaced in the Internet. Here’s what you should do about it.

Security researchers found several ways to compromise hardware cryptocurrency wallets made by Ledger and Trezor.